
Great communication strengthens cybersecurity awareness
As organisations strive to achieve ever-heightened levels of cybersecurity it is clear that in many cases the human element remains the weakest link in the cyber defence chain. While a comprehensive suite of cybersecurity products, including state of the art firewalls, endpoint protection and response tools and sophisticated email filtering goes a long way towards bolstering defence, we mustn’t forget how ongoing education and communication strengthens cybersecurity awareness.
In and of itself, this advice is nothing new. Every organisation should have some form of regular security information, advice and training available to their employees. With this in mind, how is it that phishing and its various derivatives remains far and away the number one method for cybercriminals to infiltrate networks?
Perhaps then, it isn’t an issue of a knowledge deficit but rather how this information is communicated. Here are a few key principles you can integrate into your communications strategy to ensure that you are getting the message across:
1 – Understand your employees
Take the time to discover where your employees currently stand. What cybersecurity concerns and fears to they have? Exactly what is their current level of awareness of the modern threat landscape? Once this information has been obtained it gives employers a good base to proceed by challenging these preconceptions in a way that is most likely to create resonance and understanding.
Not only will this assist in ensuring that all communication is correctly pitched and positioned, by integrating a culture of two-way communication you will further bolster your organisation’s security posture through continuous improvements.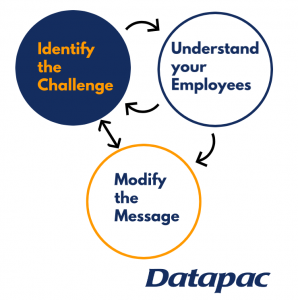
2 – Use appropriate language
Its important to use language which is easy, accessible and comprehensible for all users. While not universally the case, oftentimes those tasked with creating and implementing internal security awareness programmes and policies will have a greater depth of knowledge on the topic than the average employee. When designing communications, never assume that everyone is as up-to-speed as you on the latest industry terms and jargon.
3 – Avoid information overload
Bombarding employees with information in the form of long, laborious, overly complicated security documents can easily result in the following negative outcomes:
A) People view the advice and information as too complex for them to comprehend and so they don’t even attempt to.
B) Some will become heavily invested in trying to understand and implement everything, which could lead to errors occurring from over-analysis.
Instead, when designing policy at a high level, take the time to identify the cybersecurity musts and focus on them. A few common examples would be:
- If a link looks at all dubious, don’t open it.
- Get in the habit of hovering your mouse cursor over hyperlinks to reveal the true destination URL. If this reveals a true URL the length of War and Peace definitely don’t click it!
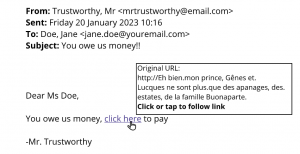
- Know who you need to alert when suspected security threats are noticed.
- How do you notify them? Remember, if you have suspicions that a link contains malware, the last thing you want to do is spread it around the organisation by directly forwarding it. Instead, take a screenshot of the full email and send it to the appropriate team for further investigation.
4 – Repeat and repackage
When the musts have been identified, take the time to plan out a communications strategy that involves regular, short repetition of these central tenets in alternative ways. Everyone is different and while the standard email newsletter may resonate well with one person it may have no impact on another. A good communications mix could include:
- Regular email newsletters
- Physical signs and posters around the premises
- An easily accessible and clearly labelled library of advice and information on the organisation’s intranet
- Short internally available on-demand videos
- Small group catch ups, be they in person or remotely using tools such as Microsoft Teams, between employees and the organisation’s cybersecurity and compliance experts.
 5 – Consider colour-coding
5 – Consider colour-coding
It could be useful to adopt distinct colour-coding to cybersecurity messaging and brand them accordingly. The red, amber and green of the traffic light system is already universally know and understood and could be used in the following way:
Red – URGENT! The organisation is actively experiencing a security breach and employees should act accordingly.
Amber – CAUTION. Due to external events and circumstances it is expected that the rate of phishing attempts will rise.
Green – INFORMATIVE. Useful tips, policy updates and reiteration of one or more of the identified musts.
6 – Add employee value through cyber vigilance
It must be noted that in order to enhance and strengthen the human element of an organisation’s cybersecurity we are effectively asking and imposing further tasks and requiring more day-to-day mindfulness from people. This is an absolute necessity in the modern digital age and most employees will understand the need. However, it doesn’t hurt to add value to the employee’s experience through cyber vigilance. For example, an organisation could take the time to compile informative assets and resources which people can use to bolster their cyber-defence in their personal lives. This could involve helpful tips on how to protect one’s home computer network, best practices to keep children safe online, how to scan for viruses on their home devices etc.
Not only will this provide a valid answer to the question of “What’s in it for me?”, but it also encourages people to become more holistically involved and mindful of cyber threats.
7 – Bring the threat to life
Put the nature of the threat into real terms by regularly sharing real-life examples and scenarios which employees may find themselves in. Simply communicating the bare facts, figures, do’s and don’ts can oftentimes be overly abstract. Real-life examples and scenarios can go a long way towards assisting with comprehension and can be key to communication strengthening cybersecurity awareness.
8 – Culture, culture, culture
Although briefly mentioned in an earlier point, it bears merit to highlight the vital role that the underlying culture plays in keeping your organisation safe from cyber-attack. Put simply, people shouldn’t be afraid to ask questions. Executive phishing, or CEO fraud, is a common form of phishing whereby the criminals will impersonate a senior member of staff with the aim of using social pressure to intimidate other team members to perform an action, such as paying a fraudulent invoice or disclosing bank details. With a healthy culture in place, employees will feel empowered to verify suspicious communications through contacting the sender via another means of communication, such as a phone call.
If you have any concerns about your organisation’s cybersecurity and would like to speak with one of our experts, please feel free to leave your details below and a member of the team will be in touch shortly.
Follow us on LinkedIn and Twitter for more updates.
Register for upcoming events
-
 "At Barretstown, we rebuild the lives of children, and their families, affected by childhood cancer and other serious illnesses. We serve 5,000 campers a year and have 1200 volunteers each year. Communication is crucially important and Datapac has helped us to streamline, improve and ensure efficiency."
"At Barretstown, we rebuild the lives of children, and their families, affected by childhood cancer and other serious illnesses. We serve 5,000 campers a year and have 1200 volunteers each year. Communication is crucially important and Datapac has helped us to streamline, improve and ensure efficiency." -
 "Datapac has provided us with a fantastic product and world-class levels of service and support. Whenever people ask me about our experience with Datapac I’m always ready to sing their praises and I would happily recommend their services to any organisation."
"Datapac has provided us with a fantastic product and world-class levels of service and support. Whenever people ask me about our experience with Datapac I’m always ready to sing their praises and I would happily recommend their services to any organisation." -
 "For many years Datapac has been our sole supplier for the maintenance of Personal Computers and Peripherals in Ireland. Through their Service Centres in Wexford and Dublin, Datapac provides excellent support to our businesses throughout the country and consistently meets the SLA targets which we have set. The skill, expertise and experience of their engineers and other technical support personnel are of the highest standard."
"For many years Datapac has been our sole supplier for the maintenance of Personal Computers and Peripherals in Ireland. Through their Service Centres in Wexford and Dublin, Datapac provides excellent support to our businesses throughout the country and consistently meets the SLA targets which we have set. The skill, expertise and experience of their engineers and other technical support personnel are of the highest standard." -
 “The value of dealing with an HP Gold partner in this process can’t be underestimated. Datapac provide us with a local touch and can cover the full range of our IT requirements, but when there is a specific technical requirement like this, they can bring the specialist technical resources of HP to the table. HP and Datapac had a thorough discussion with us around our requirement - and had really done their homework - and then were able to provide us with a very highly specified test platform for us to prove the application on before we committed to purchase.”
“The value of dealing with an HP Gold partner in this process can’t be underestimated. Datapac provide us with a local touch and can cover the full range of our IT requirements, but when there is a specific technical requirement like this, they can bring the specialist technical resources of HP to the table. HP and Datapac had a thorough discussion with us around our requirement - and had really done their homework - and then were able to provide us with a very highly specified test platform for us to prove the application on before we committed to purchase.” -
 Datapac understands our needs and requirements and has the expertise and experience to follow through on all our requests. Our constant need to reduce costs has been assisted by Datapac's ability to suggest alternative solutions and methods whilst improving both efficiency and productivity. Our partnership with Datapac is akin to having an IT department on site that we simply could not provide ourselves.
Datapac understands our needs and requirements and has the expertise and experience to follow through on all our requests. Our constant need to reduce costs has been assisted by Datapac's ability to suggest alternative solutions and methods whilst improving both efficiency and productivity. Our partnership with Datapac is akin to having an IT department on site that we simply could not provide ourselves.